TL;DR
A social engineering campaign has exploited the Obsidian note-taking app to deliver a new, sophisticated RAT called PHANTOMPULSE. Attackers use shared vaults and malicious plugins, with the malware using blockchain to hide C2 communication. The attack targets finance and crypto sectors on Windows and macOS.
Cybersecurity researchers have confirmed that a targeted social engineering campaign is exploiting the Obsidian note-taking application to deploy a previously undocumented remote access trojan named PHANTOMPULSE, primarily targeting professionals in finance and cryptocurrency sectors on Windows and macOS.
The attack involves threat actors posing as venture capitalists on platforms like LinkedIn and Telegram, engaging victims in conversations that lead to shared Obsidian vaults. The malicious campaign hinges on convincing users to enable community plugins within Obsidian, which then executes malicious scripts to deploy the RAT.
Once activated, PHANTOMPULSE can perform keylogging, screen capturing, file exfiltration, and remote command execution. It employs a novel command-and-control mechanism that queries the Ethereum blockchain for instructions, embedding the C2 address within blockchain transactions, making it highly resistant to takedown efforts.
Why It Matters
This development underscores a sophisticated evolution in malware delivery, exploiting legitimate productivity tools and blockchain technology to evade detection and disruption. The targeted nature and use of blockchain for C2 communications make this threat particularly challenging for defenders, especially in high-stakes financial and crypto environments.

Python Scripting for Cybersecurity: Linux Edition: Volume 2 – Log Analysis, Network Visibility, and Threat Detection with Hands-On Python Projects
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Background
Obsidian is a popular note-taking app used by many professionals for secure documentation. Recent campaigns have increasingly targeted collaboration features and third-party plugins to deliver malware. The PHANTOMPULSE RAT is a new, advanced payload that demonstrates the growing sophistication of cyber threats leveraging legitimate tools and decentralized infrastructure.
“The use of blockchain for command-and-control makes PHANTOMPULSE highly resistant to traditional takedown techniques.”
— Cybersecurity researcher
“Users should exercise caution when enabling community plugins, especially from untrusted sources.”
— Obsidian security team

Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What Remains Unclear
It is not yet clear how widespread the campaign is or how many victims have been compromised. Details about the full scope of the malware’s capabilities and the specific infrastructure used for command-and-control are still emerging. Additionally, attribution to specific threat actors remains unconfirmed.

Klein Tools VDV526-200 Cable Tester, LAN Scout Jr. 2 Ethernet Tester for CAT 5e, CAT 6/6A Cables with RJ45 Connections
VERSATILE CABLE TESTING: Cable tester for data (RJ45) terminated cables and patch cords, ensuring comprehensive testing capabilities
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
What’s Next
Cybersecurity teams are expected to enhance monitoring for Obsidian activity, especially regarding plugin installations and blockchain-related network traffic. Researchers will continue analyzing the malware’s infrastructure and develop detection signatures. Further disclosures may reveal the scope and impact of the campaign.
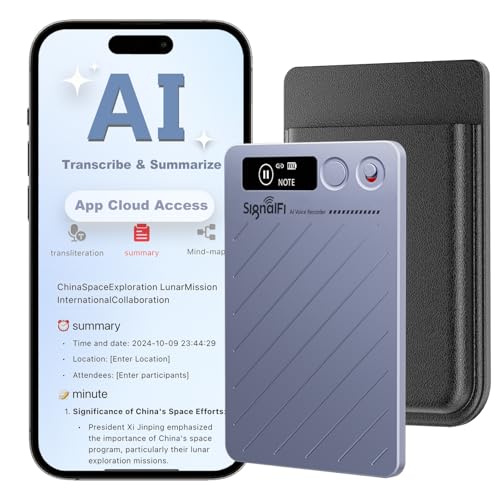
AI Voice Recorder w/Case, AI Note Taker & App Control, AI Transcription and Summary, Noise Cancellation, 152 Languages, 64GB Digital Audio Recorder for Meetings, Lectures & Calls
7 Advanced AI Models: This AI voice recorder transcriber is powered by 7 advanced AI models to deliver…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Key Questions
How does the malware infect victims through Obsidian?
The infection occurs when users open a malicious shared vault and are tricked into enabling community plugins, which execute malicious scripts to deploy the RAT.
What makes PHANTOMPULSE difficult to detect?
It uses in-memory payloads, exploits legitimate plugin features, and employs blockchain-based C2 communication to evade traditional detection methods.
Who is most at risk from this attack?
Professionals in finance and cryptocurrency sectors who use Obsidian for sensitive data are primary targets due to the high value of their information.
What steps can users take to protect themselves?
Users should avoid enabling untrusted plugins, disable auto-sync for unknown vaults, and remain vigilant against social engineering tactics. Organizations should enforce application control and network monitoring for blockchain activity.









